Private investigation services
Private Research Services Private investigation services are a valuable help for both individuals and businesses. They provide a range of services, from property investigations to

Private Research Services Private investigation services are a valuable help for both individuals and businesses. They provide a range of services, from property investigations to

Our company was certified for 2021 as a “high reliability company” with the O.T.I. method.The certificate is awarded to professionals who are characterized by excellent

Ios vs Android : Much has been said about choosing the right mobile for the needs of each user. Most people seem to be leaning
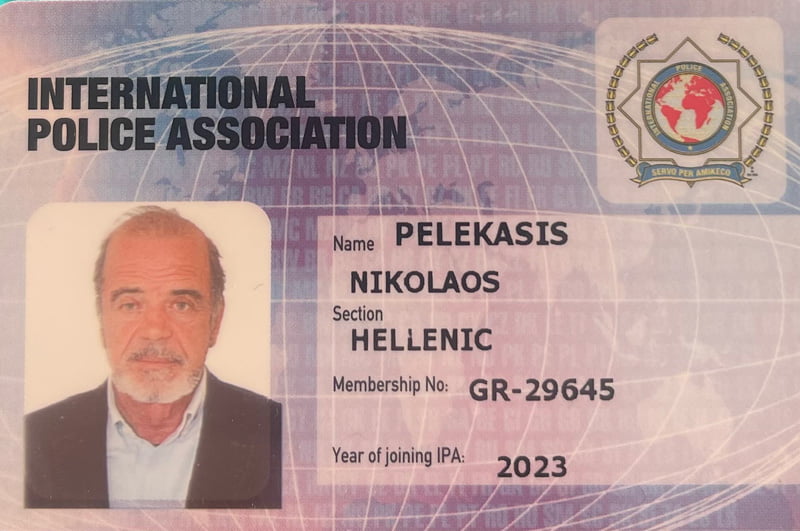
Nikos Pelekasis and Associates, a private investigation agency in Athens, has been operating successfully since 1980 until today. Our staff consists of highly trained professionals who remain constantly up-to-date on both new technological developments and the latest counter-monitoring practices. Through regular seminars and trainings both in Greece and abroad, we constantly strive to improve the level and efficiency of our services.